Minions for a distributed Internet
Proposal · Under active design · Not yet open for enrollment
This page describes a future capability. The operator program is not yet open. If you are interested in participating as an early operator and helping shape the design, reach out. Operator feedback will directly influence the program structure and compensation model.
The modern internet is increasingly centralized. A small number of providers now control where data is stored and how it is served. While this has made infrastructure easier to use, it has also introduced significant technical risk: outages can take large portions of the web offline, and shared infrastructure creates common points of failure. A more resilient model distributes storage across independent operators, so availability does not depend on any one system or organization. By spreading data across many nodes, a distributed network improves durability, fault tolerance, and long-term accessibility.
Centralization also concentrates control. When storage and delivery are handled by a small set of providers, their policies (and the policies imposed on them) can shape what remains accessible. These systems become natural targets for attackers, and points of leverage for governments seeking to censor information or monitor activity at scale. A decentralized approach reduces that leverage. By distributing data across independent participants, it becomes more difficult to suppress access, enforce unilateral policy decisions, or conduct broad surveillance. In this way, a decentralized internet acts as a hedge against both technical failure and centralized control.
A decentralized internet also invites participation. Rather than relying solely on large platforms, anyone can contribute storage and bandwidth directly to the network. The system is designed to work across a wide range of environments. Datacenter operators can integrate it into existing infrastructure and utilize spare capacity efficiently, while individuals can run nodes on everyday hardware. This flexibility allows the network to grow organically, powered by both professional infrastructure and independent operators.
Pushing the state of the art
Existing storage systems tend to fall into two categories.
On one end are traditional infrastructure where storage may be reliable but ultimately based on a trust relationship. Storage nodes may be operated by the same organization as those who rely on them, or perhaps a contracted third party, and they work together to build a common product.
Example: a website that relies on a PostgreSQL database cluster operated by the company DBA.
On the other end are fully decentralized networks. These systems assume no trust between participants and rely on economic incentives and cryptographic proofs to enforce correct behavior. In practice, many of these networks are built around token-based models, where participation and pricing are mediated by a native asset. As a result, both the cost of storage and the incentives for operators can be influenced by market dynamics beyond the underlying utility of the system. Furthermore, while these networks have a successful track record of onboarding data archival, they do not operate well as a general purpose storage layer.
Example: Filecoin, Sia, Storj
The Minion Network takes a different approach. It uses lightweight, cryptographic verification to ensure that storage nodes are behaving correctly, but avoids the complexity of fully trustless coordination by introducing a trusted verifier. This allows the system to remain efficient and practical, while, critically, the actual storage component is operated by independent, untrusted participants. The result is a middle ground that adopts the best traits of a fully distributed network, and adds the access speed we expect from a traditional storage system.
How the Minion Network enforces correct behavior
The Minion Network enforces correct behavior in several ways, starting with pin assignments. Every file pinned through the system is simultaneously assigned to multiple storage nodes. This serves three purposes:
- Availability – files remain pinned even if some nodes go offline.
- Performance – content can be served from multiple sources, improving responsiveness.
- Anti-cheating – assigning the same file to multiple nodes strengthens the challenge–response verification system (described below).
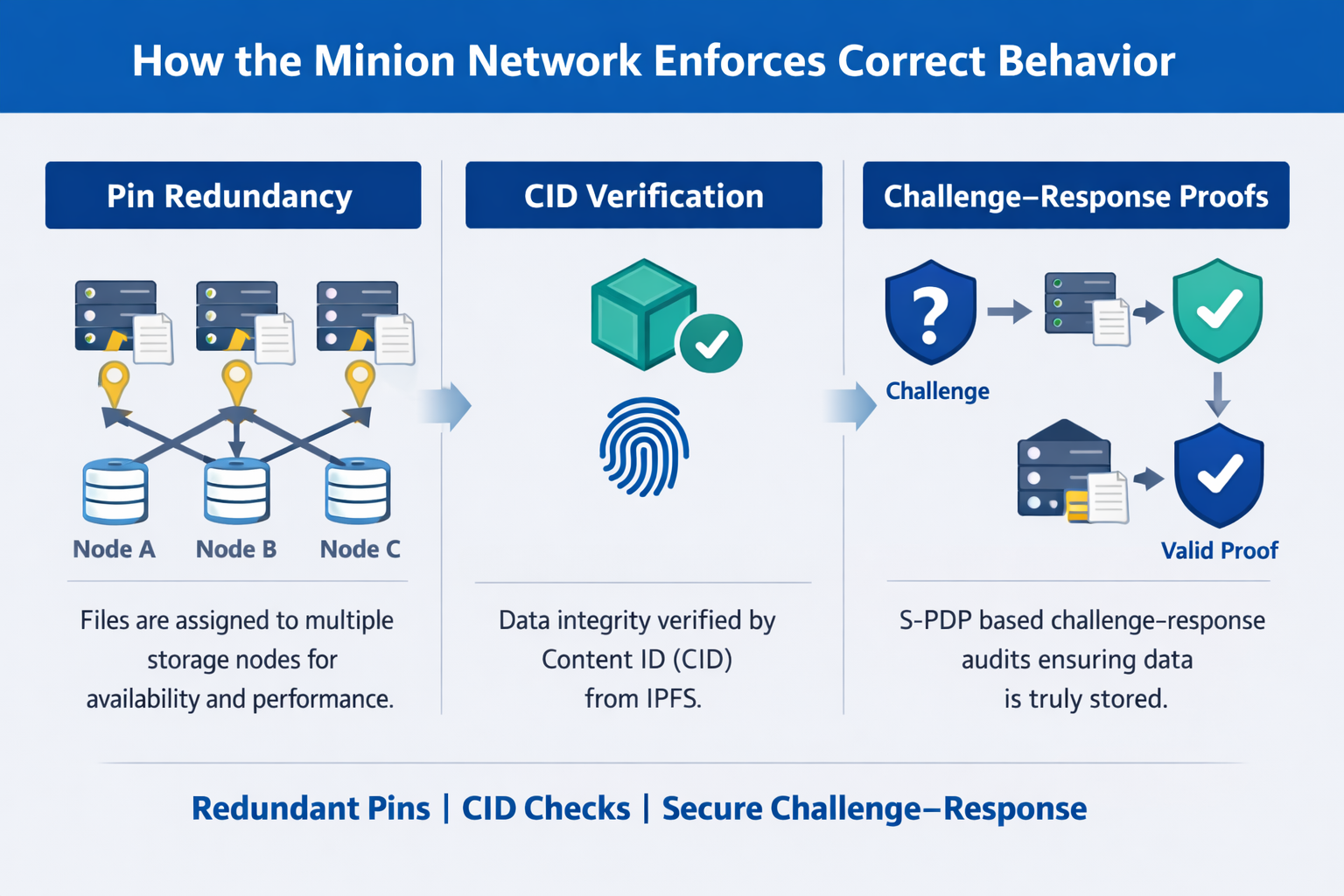
Data integrity is guaranteed via CID checking, which we inherit directly from IPFS. Thanks to IPFS, we can immediately detect accidental or malicious corruption of stored content.
To verify that nodes are actually storing the assigned data, the network uses lightweight challenge–response proofs based on Secure Provable Data Possession (S-PDP). This protocol, originally developed by researchers at Johns Hopkins and Google, has been extended in our system to operate efficiently over IPFS DAGs. S-PDP provides strong guarantees while remaining lightweight enough to issue verification challenges over epochs of just a few seconds, making the system both secure and responsive.
Anti-Collusion and Incentives
Beyond basic verification, the Minion Network enforces honest behavior through anti-collusion and incentive mechanisms. Nodes do not choose which files they store; assignments are distributed by the network, reducing the opportunity for coordination between potentially dishonest nodes. Verification challenges can span multiple files simultaneously, making it difficult for colluding nodes to pass checks without actually storing the required data.
In addition, the network tracks timeliness and correctness of responses. Nodes that attempt to game the system—for example, by fetching data on-demand instead of storing it—respond more slowly and receive lower rewards. Reputation scores are updated continuously, penalizing nodes that refuse assignments or fail proofs and prioritizing those that store and serve files reliably. By combining these mechanisms, the Minion Network ensures that the most profitable strategy for any participant aligns with honest, consistent behavior.
Incentive-Compatible Enforcement
The Minion Network couples its reward function directly to the outcomes of the challenge–response protocol, making incentives and enforcement indistinguishable. Compensation is computed deterministically from verifiable metrics: correctness of responses, response latency, and historical reliability. This construction induces an incentive-compatible system in which the strategy that maximizes expected reward is to store assigned data locally and serve it promptly.
The precise reward function remains an area of active research and iteration. However, the current design direction is to provide a base payment to the first N valid responders to a challenge, ensuring predictable participation incentives, combined with a time-decaying bonus that rewards lower-latency responses. In this model, earlier correct responses receive higher compensation, with rewards decreasing as response time increases within the challenge window.
Any deviation from correct behavior is economically penalized by design. Strategies that attempt to externalize storage—such as retrieving data from other nodes at challenge time—incur additional network latency and variability. These factors reduce both immediate payouts and accumulated reputation, which in turn lowers the probability of receiving future assignments. Over repeated interactions, such strategies are strictly dominated by honest storage and prompt response.
As a result, the network enforces correct behavior without requiring trusted participants or discretionary oversight. Instead, it relies on a closed feedback loop between verifiable performance and reward allocation, ensuring that rational operators converge toward honest participation as the equilibrium strategy.
Expressing Interest
If you would like to participate as an early operator or provide feedback on the program design, email us at hello@pinioneng.com. No commitments implied — this is an early interest form only.